Protect Your Entire Environment From Growing OT Threats
Our ICS Cybersecurity Consulting Service provides tailored strategies to secure industrial control systems and operational technology.
We offer expertise in two principal standards: ISA/IEC 62443 for organisations needing security measures specifically for ICS in manufacturing, energy, and utilities and NIST SP 800-82 for those requiring comprehensive guidelines applicable across various industries and environments.

Who Needs This Service
- Organisations operating in the industrial sector are looking for an internationally recognised cybersecurity benchmark (ISA/IEC 62443).
- Broader industries require an auditable and adaptable cybersecurity framework (NIST SP 800-82).

What We Deliver
Focus on safeguarding industrial automation and control systems with a standard recognised for its detailed guidelines and international collaboration.
Implement robust security practices with a guide to ICS cybersecurity, including risk management, security program development, and incident response.
The Benefits to Your Business
Specialised Expertise
Gain insights from specialists in ICS security to protect critical infrastructure.
Strategic Risk Management
Enhance your capacity to manage cyber risks with best practice frameworks tailored to the industrial sector.
About Excite Cyber
We are cyber, technology and business experts who asked ourselves, what would the world look like if you could be truly fearless with your business, and what if the very best cyber expertise could be integrated into robust, outcome-focused technology solutions?
Our approach is to be deeply consultative and deliver pragmatic and strategic services that work for your business. With an uncompromising approach to cyber security, we deliver solutions that will get you excited about the potential for technology all over again.
Our Latest Perspectives

Excite Cyber ECDC Threat Intelligence Report – Q4 2025
The fourth quarter of 2025 demonstrated an escalating convergence of nation-state espionage, ransomware innovation, and supply-chain exploitation across the Asia–Pacific region. As geopolitical tensions intensify and digital dependencies deepen, threat actors have pivoted from opportunistic attacks to systematic campaigns targeting trust architectures—identities, cloud infrastructure, and third-party integrations that underpin modern enterprise operations.
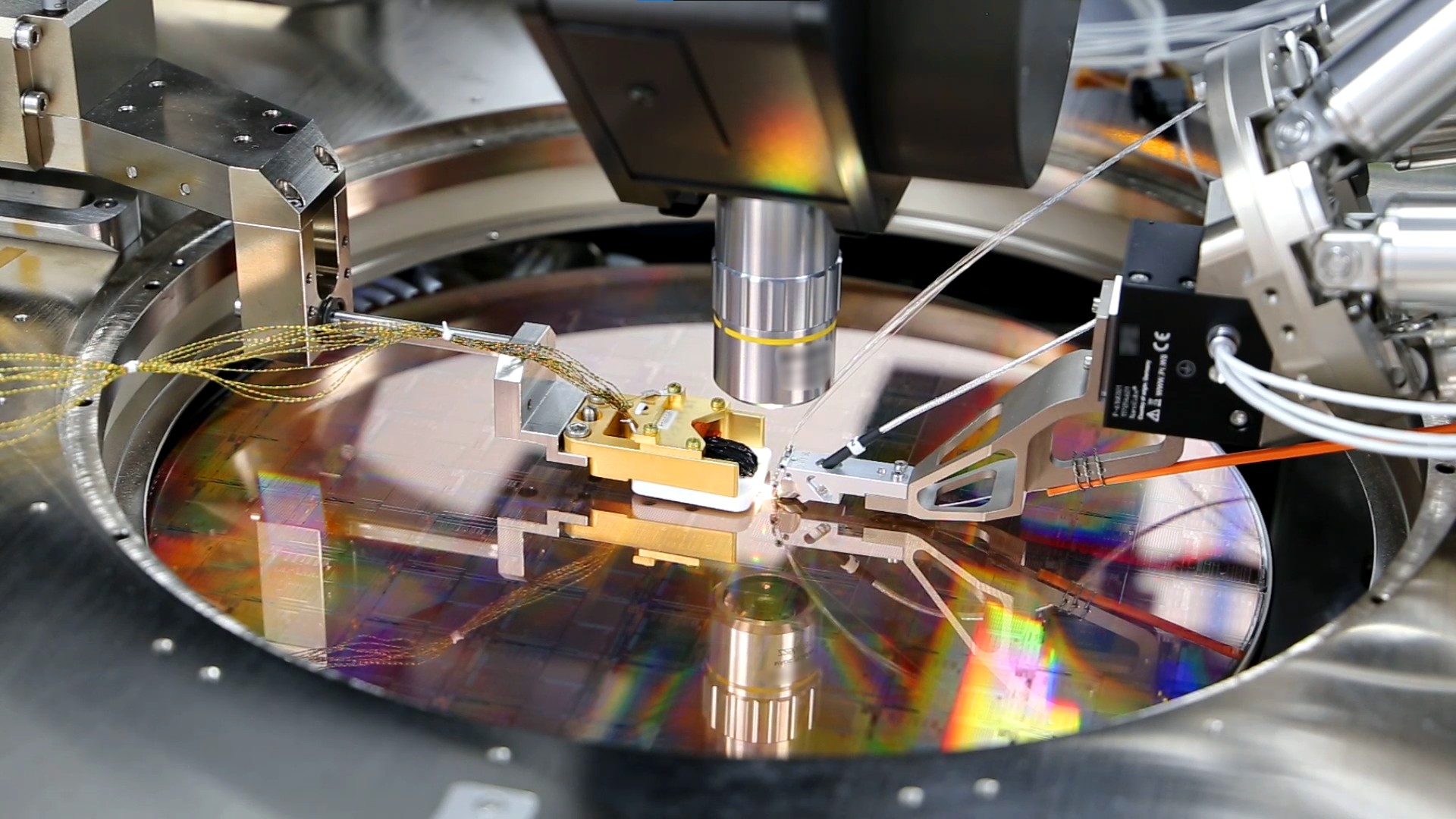
Australia Will Be A Leader In Quantum Computing: Why This Matters For Cyber Security
Quantum computing represents the next big “moon landing” moment for technological advancement. When it happens – and it will, with researchers getting ever closer to the big breakthrough – it will revolutionise industries and redefine how we engage with computing.

Why small businesses should see cyber security as a catalyst for innovation
Explore the escalating cyber security threats small businesses face and discover eight cost-effective steps to bolster IT security and foster innovation without fear.

Get Started with Excite
We are ready to collaborate with you every step of the way to protect your business and enable you to benefit from decades of experience in providing managed services.
To get started, schedule a complimentary call using the form below today.

Frequently Asked Questions
Our services are ideal for organisations within the industrial sector seeking an internationally recognised cybersecurity benchmark, specifically those adhering to ISA/IEC 62443 standards. Additionally, we cater to a wider range of industries that require a flexible and auditable cybersecurity framework, such as the one provided by NIST SP 800-82.
ICS are susceptible to various cyber threats including malware, ransomware, phishing attacks, and targeted cyber espionage. These threats can lead to unauthorised access, control system interference, data theft, and even physical damage to industrial equipment.
The shift towards modern communication technologies in ICS, such as the adoption of Internet of Things (IoT) devices, increases connectivity but also expands the attack surface. This makes ICS more vulnerable to cyber attacks and requires updated security measures to protect against new and evolving threats.
Best practices for securing ICS include conducting regular risk assessments, maintaining an accurate asset inventory, implementing defence-in-depth strategies, ensuring physical security, and establishing robust incident response plans. It’s also important to provide cybersecurity training to personnel and to work with vendors that prioritise security in their products and services.

